- Offizieller Beitrag
Package : netpbm-free
Vulnerability : insufficient input sanitizing
Problem type : local (remote)
Debian-specific: no
CVE Id(s) : CVE-2008-0554
A vulnerability was discovered in the GIF reader implementation in
netpbm-free, a suite of image manipulation utilities. Insufficient
input data validation could allow a maliciously-crafted GIF file
to overrun a stack buffer, potentially permitting the execution of
arbitrary code.
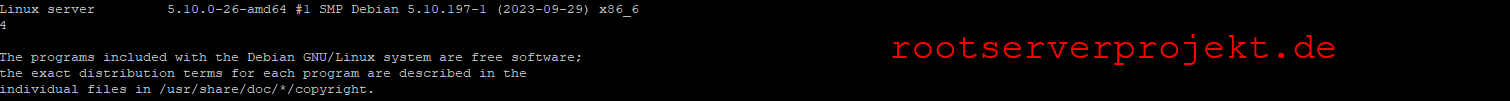
For the stable distribution (etch), these problems have been fixed in
version 2:10.0-11.1+etch1.
For the unstable distribution (sid), these problems were fixed in
version 2:10.0-11.1.
We recommend that you upgrade your netpbm packages.
Upgrade instructions
- --------------------
wget url
will fetch the file for you
dpkg -i file.deb
will install the referenced file.
If you are using the apt-get package manager, use the line for
sources.list as given below:
apt-get update
will update the internal database
apt-get upgrade
will install corrected packages
You may use an automated update by adding the resources from the
footer to the proper configuration.
Debian GNU/Linux 4.0 alias etch