- Offizieller Beitrag
Package : lighttpd
Vulnerability : DOS
Problem type : remote
Debian-specific: no
CVE Id(s) : CVE-2008-1531
It was discovered that lighttpd, a fast webserver with minimal memory
footprint, was didn't correctly handle SSL errors. This could allow
a remote attacker to disconnect all active SSL connections.
This security update fixes a regression in the previous one, which caused
SSL failures.
For the stable distribution (etch), this problem has been fixed in version
1.4.13-4etch8.
We recommend that you upgrade your lighttpd package.
Upgrade instructions
- --------------------
wget url
will fetch the file for you
dpkg -i file.deb
will install the referenced file.
If you are using the apt-get package manager, use the line for
sources.list as given below:
apt-get update
will update the internal database
apt-get upgrade
will install corrected packages
You may use an automated update by adding the resources from the
footer to the proper configuration.
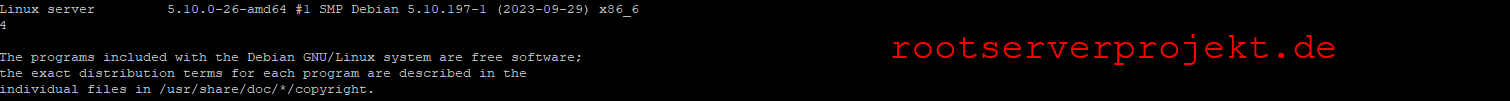
Debian GNU/Linux 4.0 alias etch