Package : apache2
CVE ID : CVE-2024-36387 CVE-2024-38473 CVE-2024-38474 CVE-2024-38475
CVE-2024-38476 CVE-2024-38477 CVE-2024-39573
Multiple vulnerabilities have been discovered in the Apache HTTP server, which may result in authentication bypass, execution of scripts in directories not directly reachable by any URL, server-side request forgery or denial of service.
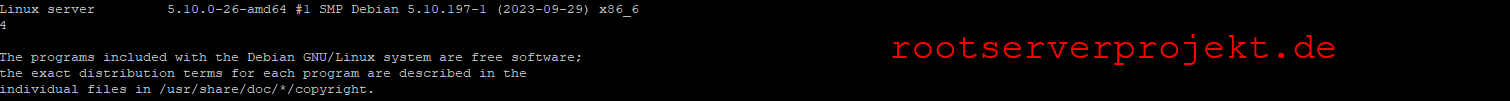
For the oldstable distribution (bullseye), these problems have been fixed in version 2.4.61-1~deb11u1.
For the stable distribution (bookworm), these problems have been fixed in version 2.4.61-1~deb12u1.
We recommend that you upgrade your apache2 packages.
For the detailed security status of apache2 please refer to its security tracker page at:
Information on source package apache2
Further information about Debian Security Advisories, how to apply these updates to your system and frequently asked questions can be found at: https://www.debian.org/security/