- Offizieller Beitrag
Package : glibc
CVE ID : CVE-2023-6246 CVE-2023-6779 CVE-2023-6780
The Qualys Research Labs discovered several vulnerabilities in the GNU C Library's __vsyslog_internal() function (called by syslog() and vsyslog()). A heap-based buffer overflow (CVE-2023-6246), an off-by-one heap overflow (CVE-2023-6779) and an integer overflow (CVE-2023-6780) can be exploited for privilege escalation or denial of service.
Details can be found in the Qualys advisory at https://www.qualys.com/2024/01/30/syslog
Additionally a memory corruption was discovered in the glibc's qsort() function, due to missing bounds check and when called by a program with a non-transitive comparison function and a large number of attacker-controlled elements. As the use of qsort() with a non-transitive comparison function is undefined according to POSIX and ISO C standards, this is not considered a vulnerability in the glibc itself. However the qsort() implementation was hardened against misbehaving callers.
Details can be found in the Qualys advisory at https://www.qualys.com/2024/01/30/qsort
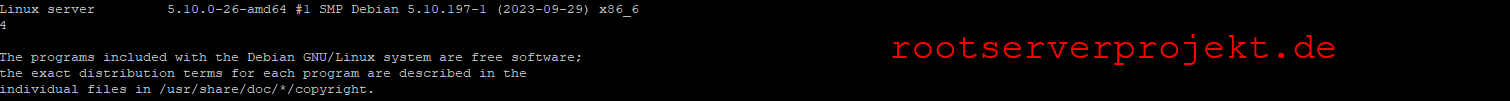
For the stable distribution (bookworm), these problems have been fixed in version 2.36-9+deb12u4.
We recommend that you upgrade your glibc packages.
For the detailed security status of glibc please refer to its security tracker page at:
Information on source package glibc
Further information about Debian Security Advisories, how to apply these updates to your system and frequently asked questions can be found at: https://www.debian.org/security/