- Offizieller Beitrag
Package : iwd
CVE ID : CVE-2023-52161
Debian Bug : 1064062
It was discovered that iwd, the iNet Wireless Daemon, does not properly handle messages in the 4-way handshake used when connecting to a protected WiFi network for the first time. An attacker can take advantage of this flaw to gain unauthorized access to a protected WiFi network if iwd is operating in Access Point (AP) mode.
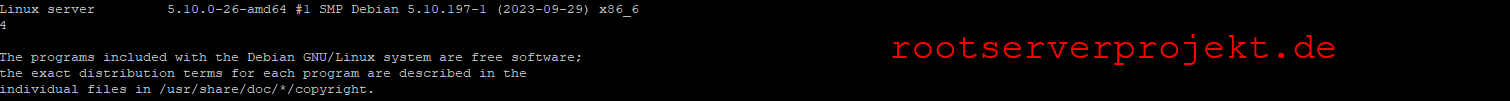
For the oldstable distribution (bullseye), this problem has been fixed in version 1.14-3+deb11u1.
For the stable distribution (bookworm), this problem has been fixed in version 2.3-1+deb12u1.
We recommend that you upgrade your iwd packages.
For the detailed security status of iwd please refer to its security tracker page at:
Information on source package iwd
Further information about Debian Security Advisories, how to apply these updates to your system and frequently asked questions can be found at: https://www.debian.org/security/